Most business operations and communication happen through email. So, there should be no surprise that cybercriminals have found new ways to exploit vulnerabilities. One such threat that has gained prominence in recent years is Business Email Compromise (BEC).
In this comprehensive guide, we will delve into the world of BEC, exploring what it is, how it works, its various types, and most importantly, how you can defend against it.
What is Business Email Compromise (BEC)?
Business Email Compromise, often referred to as BEC, is a sophisticated form of phishing attack that specifically targets organisations. The primary objective of BEC is to deceive individuals within a company into taking actions that compromise the organisation’s financial assets or sensitive information.
BEC attackers pose as trusted figures, such as executives or vendors, to manipulate recipients into carrying out their malicious intentions.
This threat has seen a significant uptick in recent years, primarily due to the surge in remote work. In fact, the FBI received nearly 20,000 BEC-related complaints last year alone.
Types of Business Email Compromise scams

BEC attacks come in various forms, each designed to exploit different vulnerabilities within an organisation. Here are some common types of BEC scams:
Data Theft
Cybercriminals may initiate BEC attacks by targeting the HR department to steal confidential company information, like employee schedules or personal phone numbers. This stolen data can be leveraged in subsequent BEC scams to make the deception appear more convincing.
False Invoice Scheme
In this type of BEC scam, the attacker poses as a legitimate vendor that your company does business with. They send a fake invoice, often meticulously crafted to resemble a genuine one, with minor alterations such as a slightly different account number. Alternatively, they may claim that their bank is under audit and request payments to a different account.
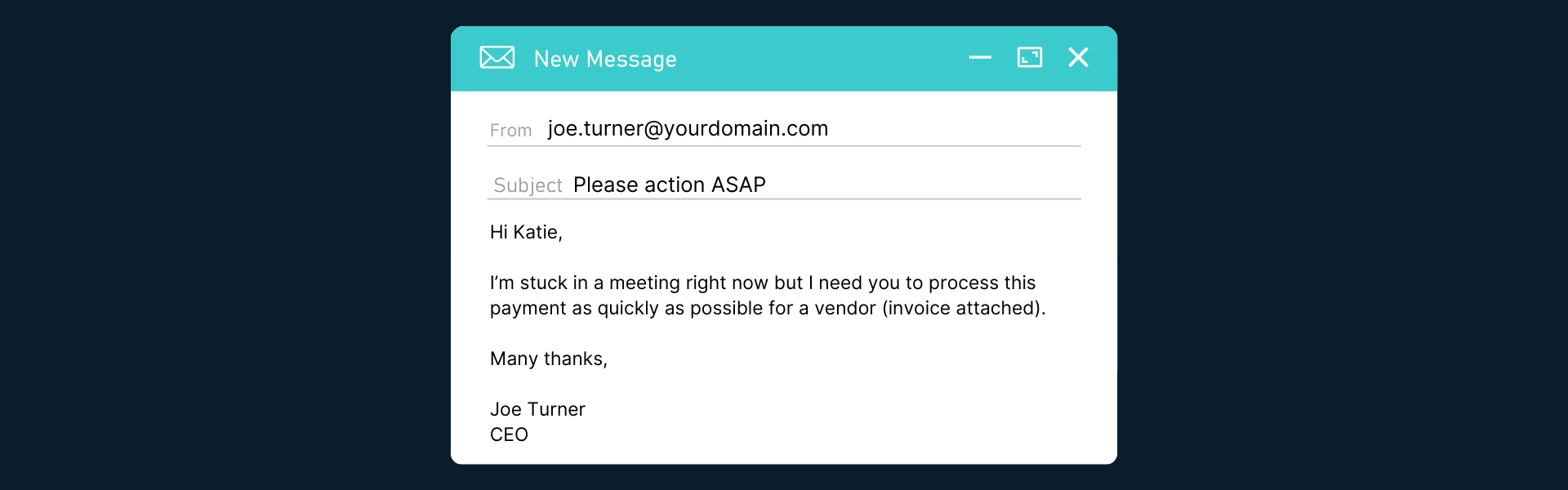
CEO Fraud
Scammers either spoof or compromise a CEO’s email account and then instruct employees to make purchases or send money via wire transfers. They might even ask employees to purchase gift cards and provide photos of the serial numbers.
Lawyer Impersonation
In this scam, attackers gain unauthorised access to a law firm’s email account and send clients fake invoices or links to pay online. While the email address may appear legitimate, the bank account provided is fraudulent.
Account Compromise
Cybercriminals use phishing or malware to gain access to a finance employee’s email account, such as an accounts receivable manager. Once inside, they send the company’s suppliers fake invoices that request payment to a fraudulent bank account.
How do BEC scams work?
Understanding the mechanics of a BEC scam is crucial in protecting against it. Here’s a step-by-step breakdown of how a BEC scam typically unfolds:
Research and Identity Deception
Scammers thoroughly research their targets, creating a detailed profile that allows them to convincingly impersonate trusted individuals within the organisation. They may even go as far as creating fake websites or registering companies with names similar to the target.
Email Monitoring
After gaining access to the victim’s email account, scammers closely monitor email correspondence to identify potential targets for financial transactions. They study email patterns, invoices, and conversations to increase the authenticity of their deception.
Gaining Trust and Requesting Action
Once the scammer has gathered enough information, they establish trust with the target through a series of email exchanges. Eventually, they request money, gift cards, or sensitive information.
Email Spoofing
To further deceive the target, scammers may impersonate one of the parties involved by spoofing the email domain. This can involve minor alterations to the email address or sending emails “via” a different domain.
Targets of Business Email Compromise

BEC attacks can target a wide range of individuals and organisations. Common targets include:
- Executives and leaders, whose details are often publicly available on company websites.
- Finance employees, such as controllers and accounts payable staff, who have access to banking details and account numbers.
- HR managers, who possess employee records containing sensitive information.
- New or entry-level employees who may lack experience in verifying email legitimacy.
The dangers of BEC

The consequences of a successful BEC attack can be devastating for organisations. If left unchecked, a BEC attack can lead to several different outcomes.
Financial Loss
Organisations can lose hundreds of thousands to millions of pounds through fraudulent transactions orchestrated by BEC scammers.
Identity Theft
Personally identifiable information (PII) can be stolen, leading to widespread identity theft among employees and clients.
Confidential Data Exposure
BEC attacks may accidentally result in the exposure of sensitive company data, including intellectual property.
As the threat landscape continues to evolve, so do the strategies employed to protect against BEC attacks. For instance, Microsoft alone blocked a staggering 32 billion email threats in 2021, underscoring the importance of robust email security solutions.
Business Email Compromise examples
To illustrate the diversity and sophistication of BEC attacks, here are some real-world examples.
Pay This Urgent Bill
An employee in the finance department receives an email from what appears to be the CFO, urgently requesting payment for an overdue bill. However, the email is not from the CFO, but from a BEC scammer. Alternatively, the scammer may impersonate a trusted vendor and send a convincing-looking invoice.
What’s Your Phone Number?
A company executive emails an employee, requesting their phone number for a “quick task.” This seemingly innocuous request is a ploy to shift communication to a more personal medium, such as text messaging, where the scammer hopes to extract sensitive information.
Your Lease is Expiring
A scammer gains access to a real estate company’s email account and identifies ongoing transactions. They then email clients, providing a link to pay lease-related expenses or renew office leases. In some cases, scammers have swindled victims out of substantial sums of money using this method.
Top Secret Acquisition
An employee receives an email from their boss, requesting a down payment for the acquisition of a competitor. The email emphasises confidentiality, discouraging the employee from verifying the request. Given the secretive nature of mergers and acquisitions, this scam can appear legitimate at first glance.
5 tips to prevent BEC

Now that you understand the gravity of BEC attacks and their various forms, here are five best practices to help you prevent falling victim to a BEC scam:
1. Use a Secure Email Solution
Implement email solutions like Office 365 that automatically flag and delete suspicious emails or alert you when the sender isn’t verified. Additional features like advanced phishing protection and suspicious forwarding detection, available in Defender for Office 365, can further enhance BEC prevention.
2. Set Up Multifactor Authentication (MFA)
Strengthen your email security by enabling MFA, which requires an additional code, PIN, or fingerprint in addition to your password for login.
3. Educate Employees
Ensure that your entire organisation is educated about how to identify warning signs of phishing attacks, such as mismatched domain and email addresses. Conduct simulated BEC scam exercises to enhance awareness.
4. Implement Security Defaults
Administrators can tighten security across the organisation by mandating the use of MFA, imposing authentication challenges for new or risky access, and requiring password resets in case of information leaks.
5. Use Email Authentication Tools
Employ email authentication methods such as Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain-based Message Authentication, Reporting, and Conformance (DMARC) to make it more challenging for scammers to spoof your email.
Business Email Compromise protection

To protect your organisation against BEC attacks, consider adopting solutions like Microsoft Defender for Office 365, which offers the following capabilities.
Automated Email Authentication Checks
Detect email authentication standards and identify spoofing, automatically sending suspicious emails to quarantine or junk folders.
AI-Powered Anomaly Detection
Utilise artificial intelligence to model each user’s normal email patterns and flag unusual activity.
Customised Email Protection
Configure email protection settings by user, domain, and mailbox to suit your organisation’s unique needs.
Threat Investigation
Investigate potential threats, identify targets, distinguish false positives, and pinpoint scammers using Threat Explorer.
Spoof Intelligence
Employ advanced algorithms to analyse domain-wide email patterns and highlight unusual activity, enhancing your defence against email spoofing.
The best BEC protection: MXDR

An MXDR (Managed eXtended Detection and Response) solution that uses Microsoft Sentinel as its SIEM (Security Information and Event Management) can provide a formidable defense against BEC attacks.
By integrating the power of Sentinel’s advanced threat detection capabilities with the broader context of an MXDR system, organisations can enhance their ability to detect and block BEC threats effectively.
Microsoft Sentinel can analyse email-related events, user behavior, and network activity, allowing it to identify anomalous patterns or actions that are indicative of BEC scams.
Additionally, by correlating information from multiple data sources, such as email logs, network traffic, and user activities, Sentinel can uncover subtle indicators of compromise that might go unnoticed by traditional security measures.
Furthermore, the automated response capabilities of an MXDR solution can swiftly quarantine suspicious emails, block malicious IP addresses, and alert security teams to take immediate action, mitigating the potential damage caused by a BEC attack.
This integrated approach not only bolsters an organisation’s email security but also provides real-time threat intelligence and response capabilities to proactively block BEC threats before they can wreak havoc.
Now you’re ready to defend against Business Email Compromise
Business Email Compromise is a pervasive and ever-evolving threat that can have severe financial and reputational consequences for organisations.
By understanding the various forms of BEC attacks, their mechanisms, and implementing robust email security measures, you can significantly reduce the risk of falling victim to these malicious schemes.
In an era where email is the king of communication, defending against BEC is not just an option; it’s a necessity to protect your organisation’s interests and data. Stay vigilant, educate your team, and invest in cutting-edge email security solutions to protect your business from the perils of Business Email Compromise.