In August 2023, a new customer partnered with CloudGuard to improve their cybersecurity posture. Little did they know that within days of going live with our CloudGuard Protect MXDR service, a multi-stage incident lurking in their environment would be exposed.
This case study delves into the incident, highlighting the importance of rapid threat detection and automated incident response.
Discovering the threat
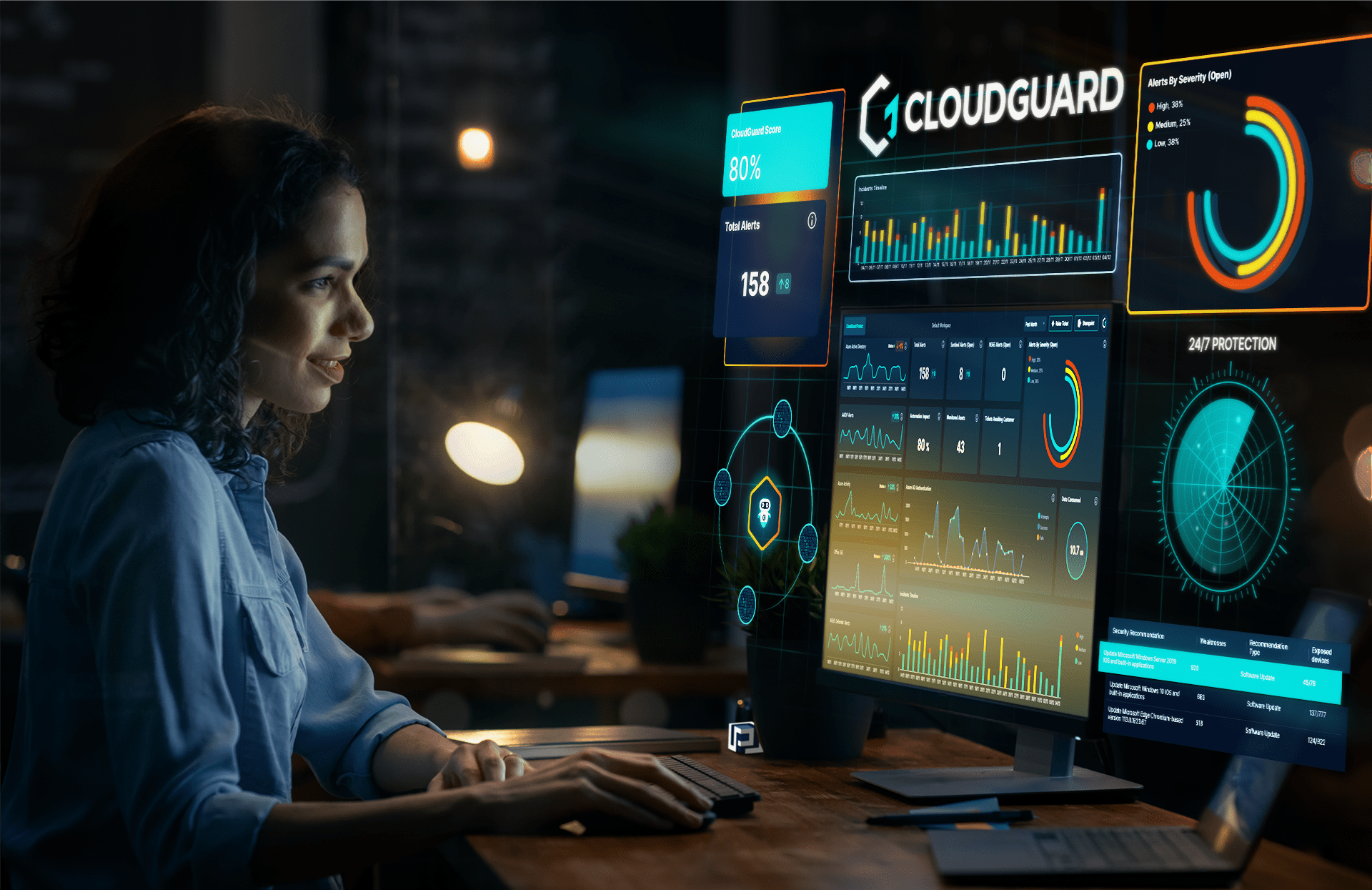
CloudGuard’s Protect MXDR service wasted no time in proving its worth. Within days of deployment, it raised the alarm on a serious security incident.
We deploy Microsoft Sentinel as a Security Incident and Event Management (SIEM) solution as part of the service. We unified all the customer’s security data into one place, so that it could be rapidly analysed thanks to its advanced algorithms.
This analysis allows us to detect suspcious patterns of anomalies in data that could be indiciative of an attack in seconds.
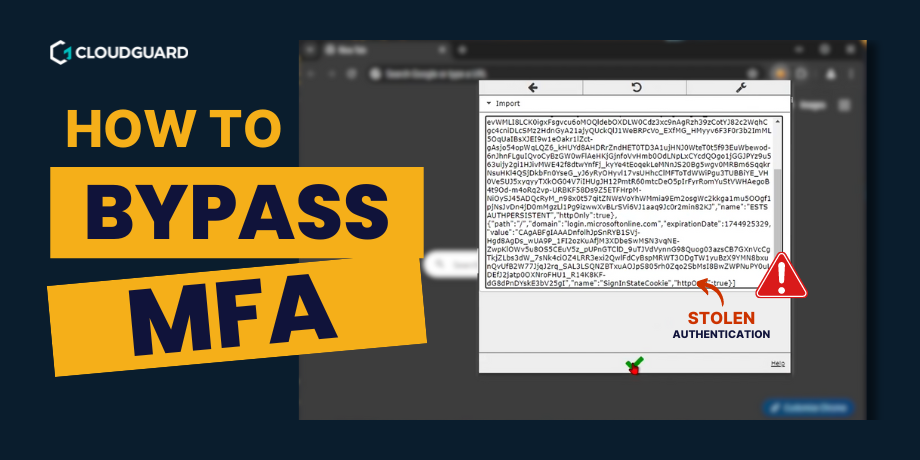
In this case, suspicious commands and tasks were cleverly concealed within Base64 encrypted payloads – making detection by traditional means nearly impossible.
Once detected, our SOC (Security Operations Centre) team quickly sprang into action.
Decoding the threat

The SOC team’s expertise was put to the test as they successfully decoded the encrypted payloads.
What they unveiled was chilling: a discreet form of malware had been making recurring attempts to manipulate the registry in the customer’s environment since March 2023.
The threat actors behind this attack were not to be underestimated.
Automated threat enrichment

One of the crucial aspects of threat detection is understanding the adversary. The problem is that this can take a human hours of painstaking research to accomplish. We reduce this process to minutes thanks to automation.
Automated threat enrichment works by continuously gathering and analysing data from various sources, including dark web forums, hacker chatter, and malware databases. This data is then correlated with the indicators of compromise (IOCs) detected in the customer’s environment.
We machine learning algorithms to identify patterns and link them to known threat actors and their tactics, techniques, and procedures (TTPs).
Here, our use of automated threat enrichment meant the malware could be swiftly linked to an attack by notorious threat actors, suspecting Emotet or Gozi to be the threat group.
Europol states: “EMOTET has been one of the most professional and long lasting cybercrime services out there. First discovered as a banking Trojan in 2014, the malware evolved into the go-to solution for cybercriminals over the years.”
This attribution provided critical context for the incident response.
Automated incident response is key
Time is of the essence in the world of cybersecurity, and CloudGuard proved its worth once again.
Within just 20 minutes of detecting the threat, CloudGuard’s automated incident response service had not only exposed the malicious command lines but also alerted the customer about the critical incident.
Furthermore, it provided detailed remediation actions, including isolating and rebuilding the affected machine.
Lessons learned
The timeline of this incident is notable. The malware had infiltrated the customer’s environment in March 2023, long before their partnership with CloudGuard began in August. This highlights the importance of continuous monitoring and detection capabilities, as threats may remain dormant for extended periods.
Moreover, the incident proves the value of an integrated MXDR service like CloudGuard’s. Rapid detection, immediate alerting, automated incident response, and actionable remediation guidance proved invaluable in mitigating the threat swiftly.
Ongoing investigation
While the immediate threat was addressed efficiently, the work is far from over.
An ongoing investigation aims to uncover how the malware gained a foothold in the environment and whether any damage was inflicted. The incident underscores the need for proactive threat hunting and post-incident analysis to strengthen defences against future attacks.
The importance of cybersecurity
The CloudGuard Protect MXDR service proved its ability in unearthing a stealthy, long-standing threat within a new customer’s environment. The incident proves the importance of robust threat detection, automated incident response, and continuous monitoring.
As organisations continue to face evolving and sophisticated threats, services like CloudGuard’s MXDR play a crucial role in improving cybersecurity defences. The swift identification and mitigation of this incident demonstrate the value of proactive cybersecurity measures in protecting sensitive data and business continuity.