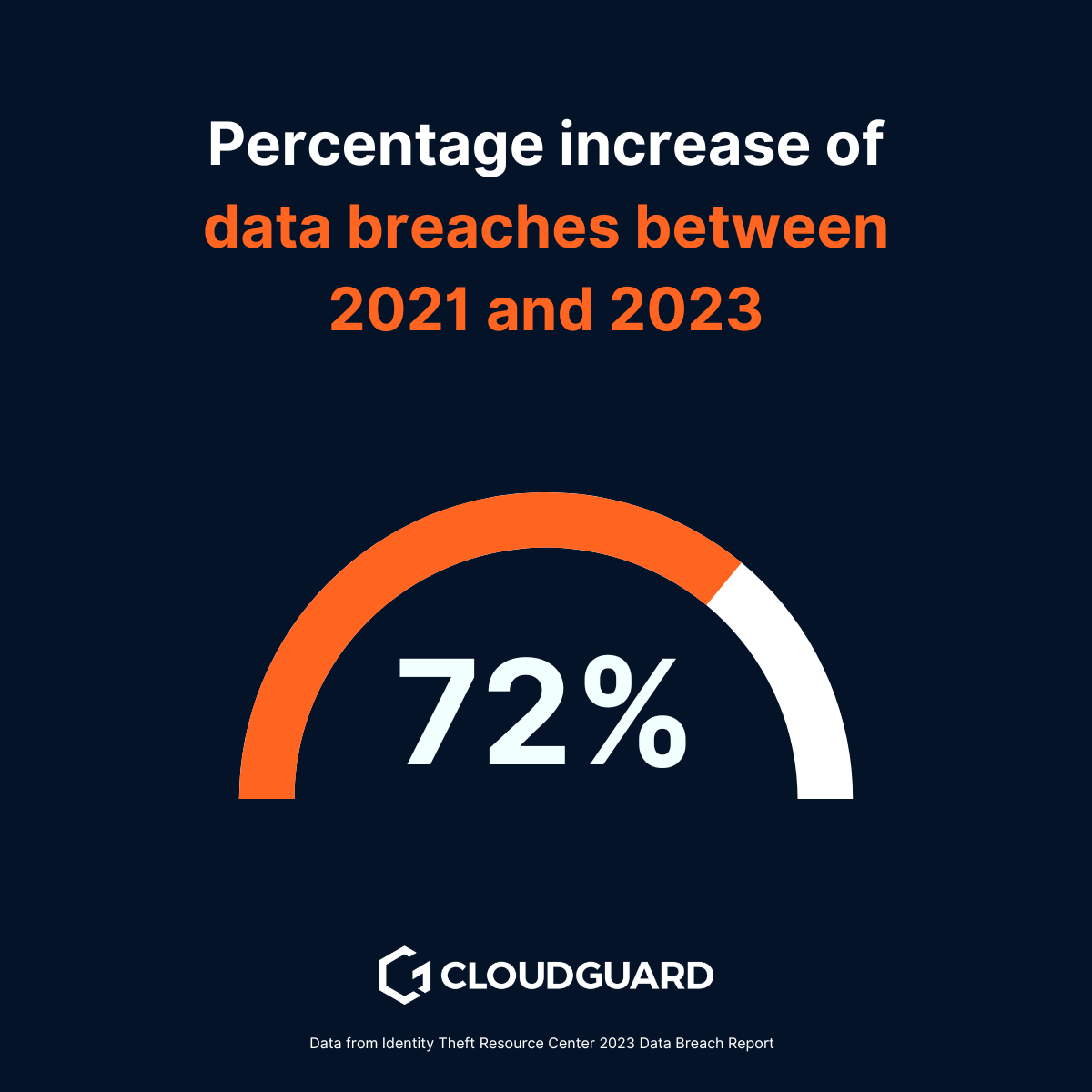
Organisations of all sizes are facing an ever-growing tide of cyber threats that put their sensitive data, intellectual property and customer trust at risk.
The conventional cybersecurity strategies that have served organisations well in the past are no longer sufficient to combat the sophisticated and relentless modern cyber attacks. It’s time for a cybersecurity revolution.
To maintain a secure environment and stay one step ahead of cybercriminals, it’s imperative that your organisations adopt a new approach to cybersecurity and embrace new technologies and solutions.
Below, we’ll explore the shortcomings of traditional cybersecurity strategies and discuss the reasons why investing in advanced solutions is critical to protecting your organisation.
The problem with conventional cybersecurity strategies
Here’s six top problems with today’s conventional cybersecurity strategies. These make the cybersecurity revolution even more crucial than ever before.
- Reactive vs proactive defence
- Signature-based detection
- Siloed solutions
- Human errors
- Inadequate incident response planning
- Failing to prioritise data protection
1. Reactive vs. proactive defence
Traditional cybersecurity strategies are often reactive, relying on identifying known threats and responding to incidents after they occur.
But is this approach sufficient?

Reactive cybersecurity is bad for business
This reactive approach can leave organisations vulnerable to new and emerging threats, as cybercriminals are constantly developing sophisticated attack techniques.
Think about it.
By the time a new threat is detected and a patch or signature is created, it may have already caused significant damage.
Here’s why.
The problem with reactive cybersecurity
Cybercriminals are constantly evolving their methods. Traditional cyber security is based on detecting threats that have already been seen and catalogued. When a new threat emerges, it takes time to recognise and combat it. During this time, companies are still exposed to potential damage.
James Babbage, Director General for Threats at the National Crime Agency, said:
Ransomware continues to be a national security threat. As this report shows, the threat is likely to increase in the coming years due to advancements in AI and the exploitation of this technology by cyber criminals.
Scary, isn’t it?
By the time a patch is developed and deployed, the threat may have already infiltrated the system and caused damage. This delay can lead to data breaches, financial losses and reputational damage.
There has to be a better way.
Proactive security is the way forward
Transformative cyber security solutions use proactive defence mechanisms such as AI and machine learning.
NCSC CEO Lindy Cameron said:
We must ensure that we both harness AI technology for its vast potential and manage its risks – including its implications on the cyber threat.
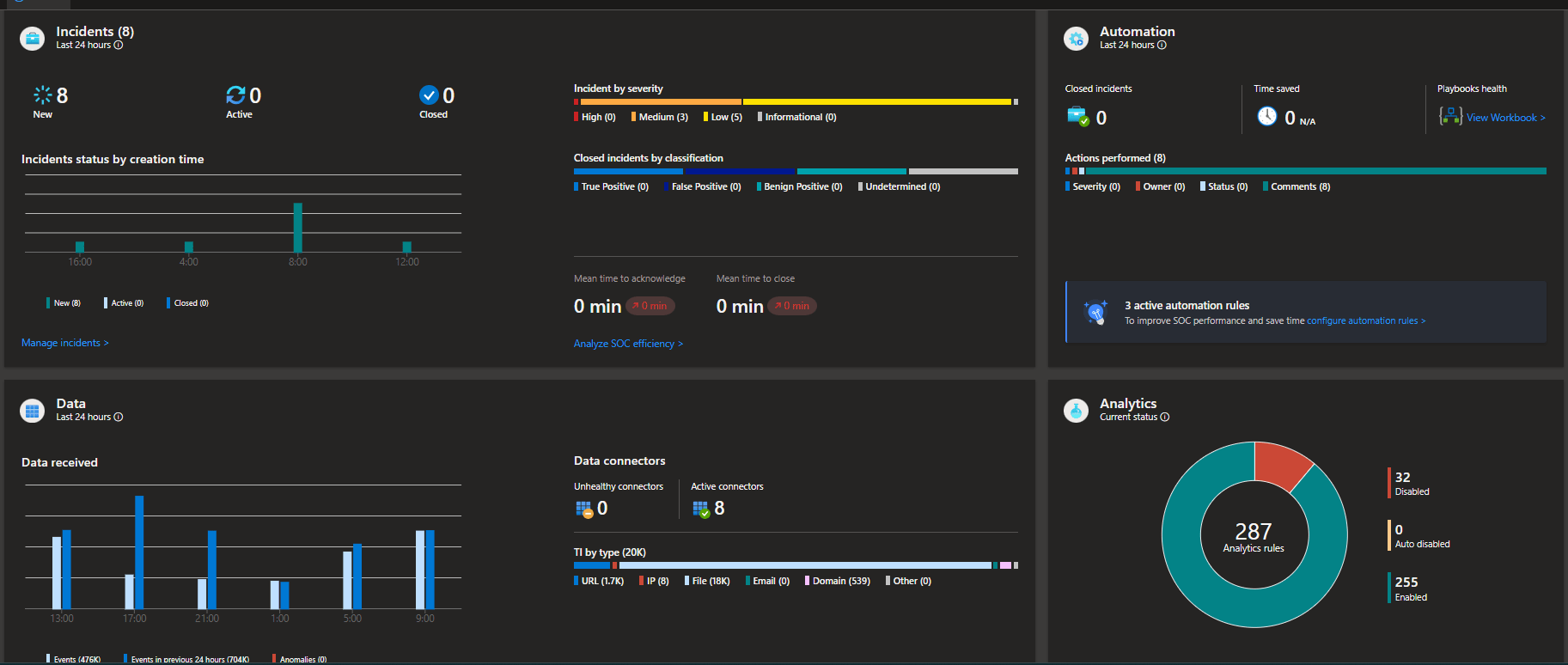
Thankfully, Security Incident and Event Management (SIEM) platforms like Microsoft Sentinel can analyse huge amounts of data in real time to detect patterns and anomalies that indicate potential cyber threats.
Imagine you could predict and prevent attacks before they happen.
With proactive defence, you can do just that. It significantly reduces the risk of data breaches and costly incidents by staying one step ahead of cybercriminals.
Isn’t that what every organisation needs?
Understanding the limitations of conventional strategies and utilising proactive solutions shows how powerful advanced technologies are in protecting against cyber threats.
2. Overreliance on signature-based detection
Conventional cybersecurity strategies often rely heavily on signature-based detection methods.
Signature-based detection methods identify cyber threats by matching them to a database of known patterns or signatures of malicious activity.
This approach relies on recognizing previously identified threats to detect and block malicious actions.
But is that enough?
Security tools compare files and code against a database of known malware signatures. While this approach can be effective against known threats, it has difficulty recognising previously unknown and sophisticated attacks.
The limitations of signature-based detection
Traditional methods rely on detecting malware that has already been identified. When new, sophisticated attacks emerge, these methods fail because the signatures are not included in the database.
As a result, these threats remain undetected.
Are you worried about the gaps?
To overcome this limitation, you should invest in behaviour-based analysis and anomaly detection.
Behavior-based analysis and anomaly detection identify cyber threats by monitoring and analysing deviations from normal or expected behavior. This approach focuses on detecting unusual activities or patterns that may indicate a security breach, rather than relying on known threat signatures.
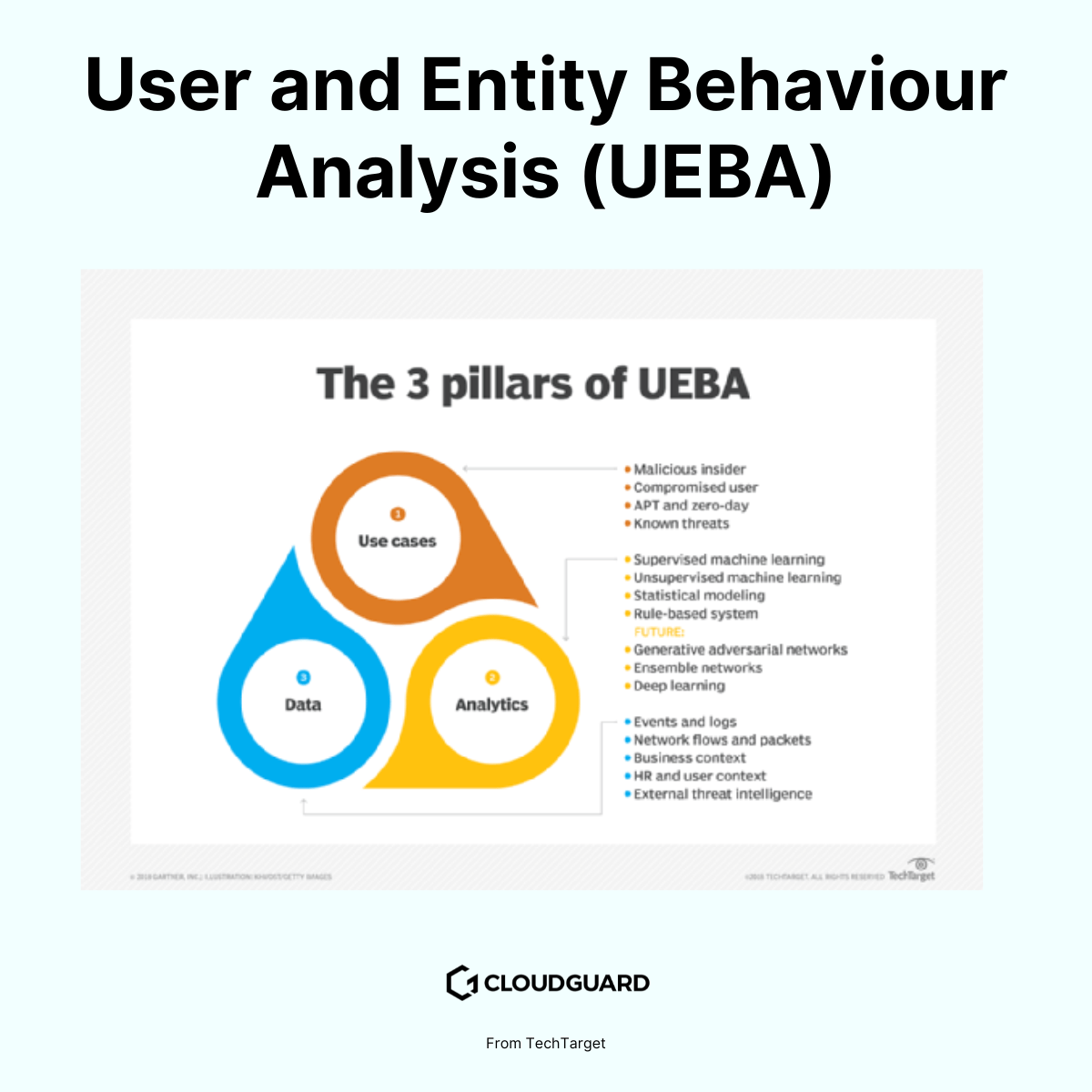
By detecting unusual activity, you can identify zero-day exploits and other new threats that evade signature-based detection.
Imagine intercepting threats before they cause damage.
By using these techniques, you improve your cybersecurity posture and effectively protect your systems from sophisticated and previously undetected attacks.
Isn’t that a smart way to stay safe?
Understanding the limitations of traditional methods and applying behavioural and anomalous detection approaches underlines the importance of advanced cybersecurity measures.
3. Lack of integration and siloed solutions
In many organisations, cybersecurity tools and solutions are used in isolation, leading to a fragmented approach to security.
Does this sound familiar?
Different security components such as firewalls, antivirus software, intrusion detection systems and endpoint protection may not communicate effectively with each other.
Understanding the issues with tech silos
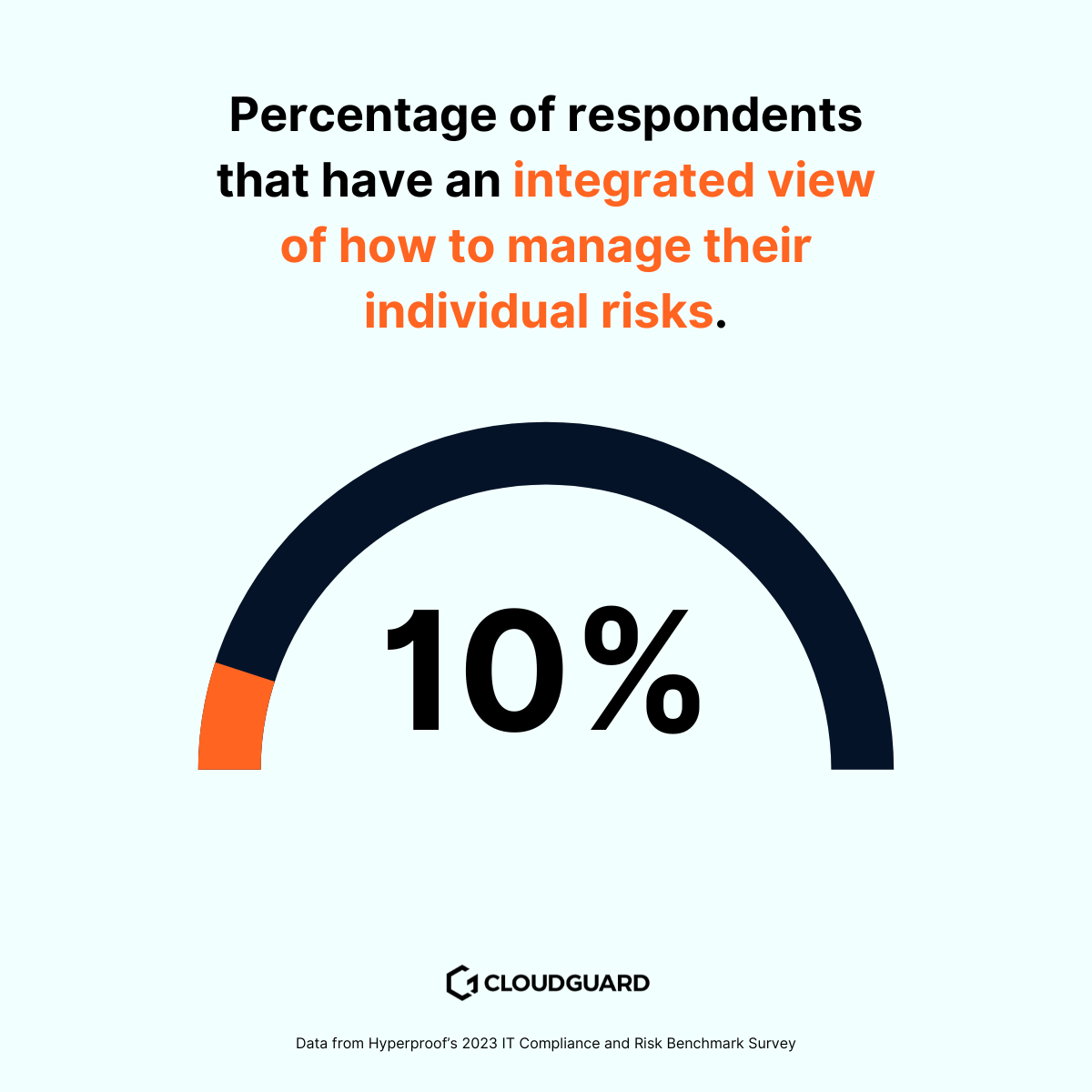
Information gaps occur, making a coordinated response to threats difficult. The 2023 IT Risk and Compliance Benchmark Report by Hyperproof found that only 10% of respondents have an integrated view of how to manage their individual risks.
When security tools work in isolation, they don’t share critical information, resulting in a disjointed defence strategy. Firewalls, antivirus programmes and intrusion detection systems working independently can lose track of each other and allow threats to slip through the cracks.
Can you recognise the problem?
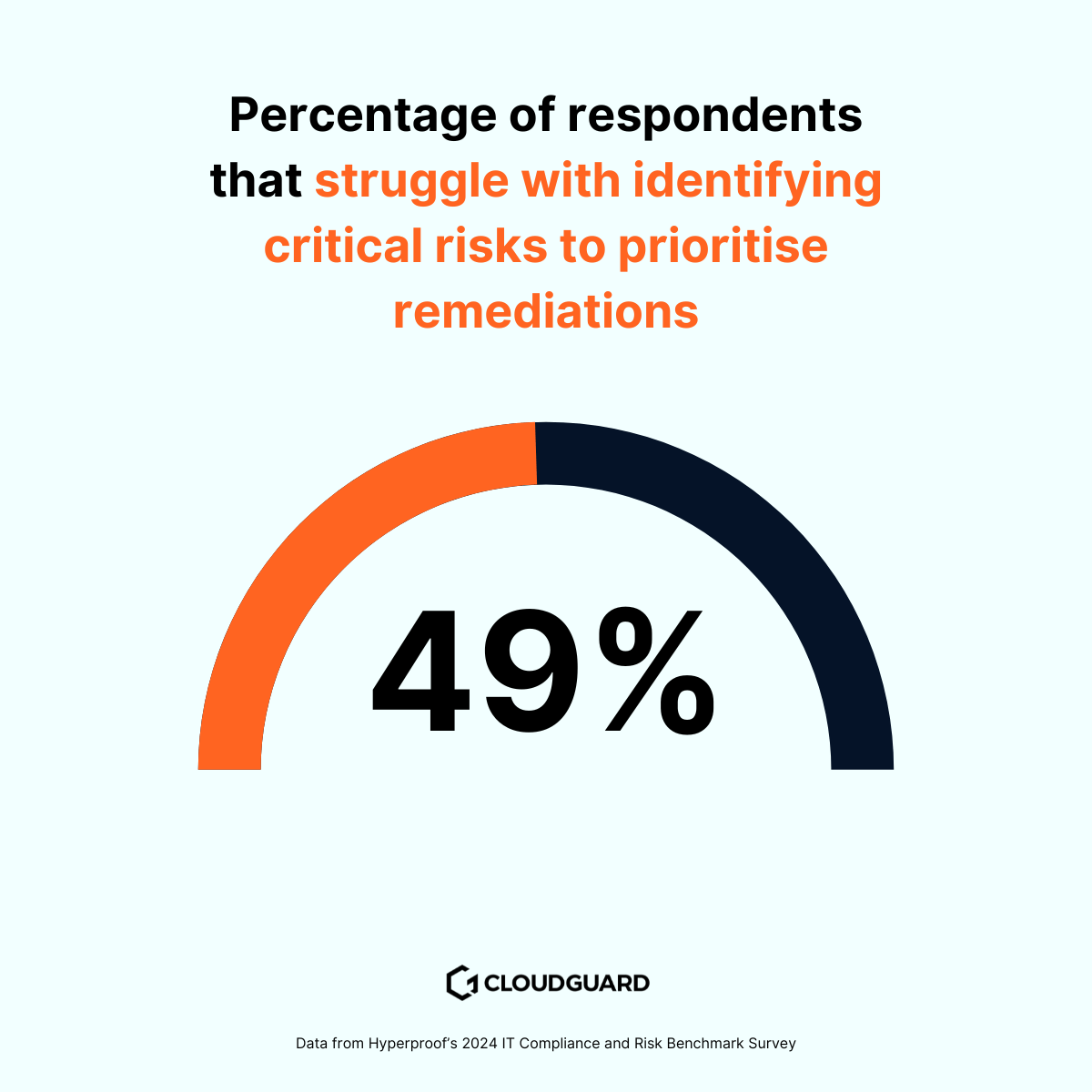
Hyperproof’s 2024 results prove this. Almost half (49%) struggle with identifying critical risks to prioritise remediations. This lack of integration makes it difficult to effectively manage and mitigate risk.
It’s clear that something needs to change.
Moving to a unified security strategy
To overcome this challenge, you should utilise integrated cybersecurity solutions that promote seamless information sharing and collaboration between security tools.
Integration enables security teams to centralise data analysis, gain a unified view of the cybersecurity posture and respond more effectively to incidents. A consolidated approach to security also streamlines workflows, reduces operational overheads and increases overall security.
Imagine all your security tools working together seamlessly.
By implementing integrated solutions, you close information gaps, improve threat response and build a more robust security framework.
Isn’t that a real game changer?
By understanding the importance of integration and opting for a unified security strategy, your organisation will be better protected against evolving cyber threats.
4. Human error and insider threats
Human error is a major challenge in traditional cyber security solutions that is often overlooked despite investments in advanced technologies.
Have you ever wondered why?
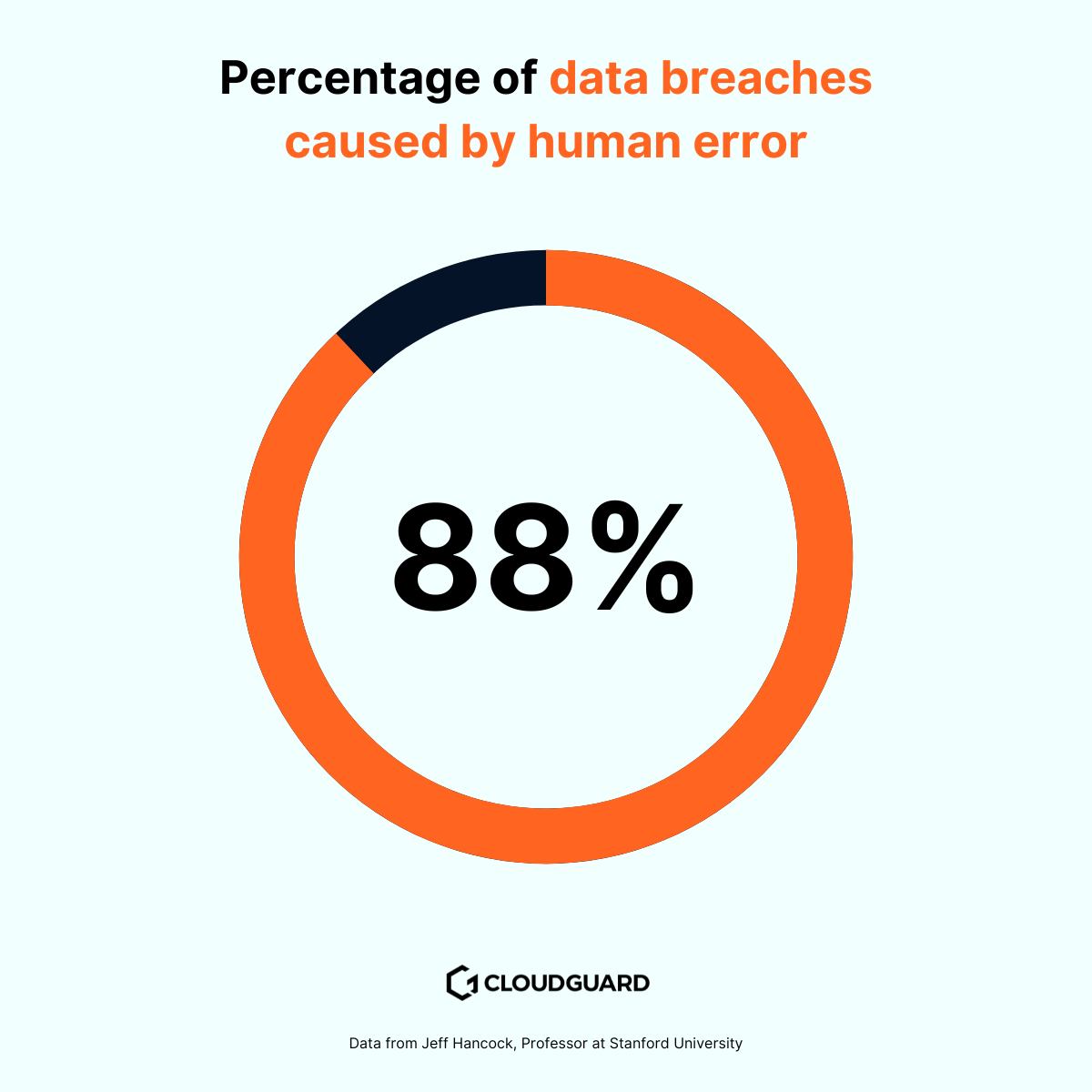
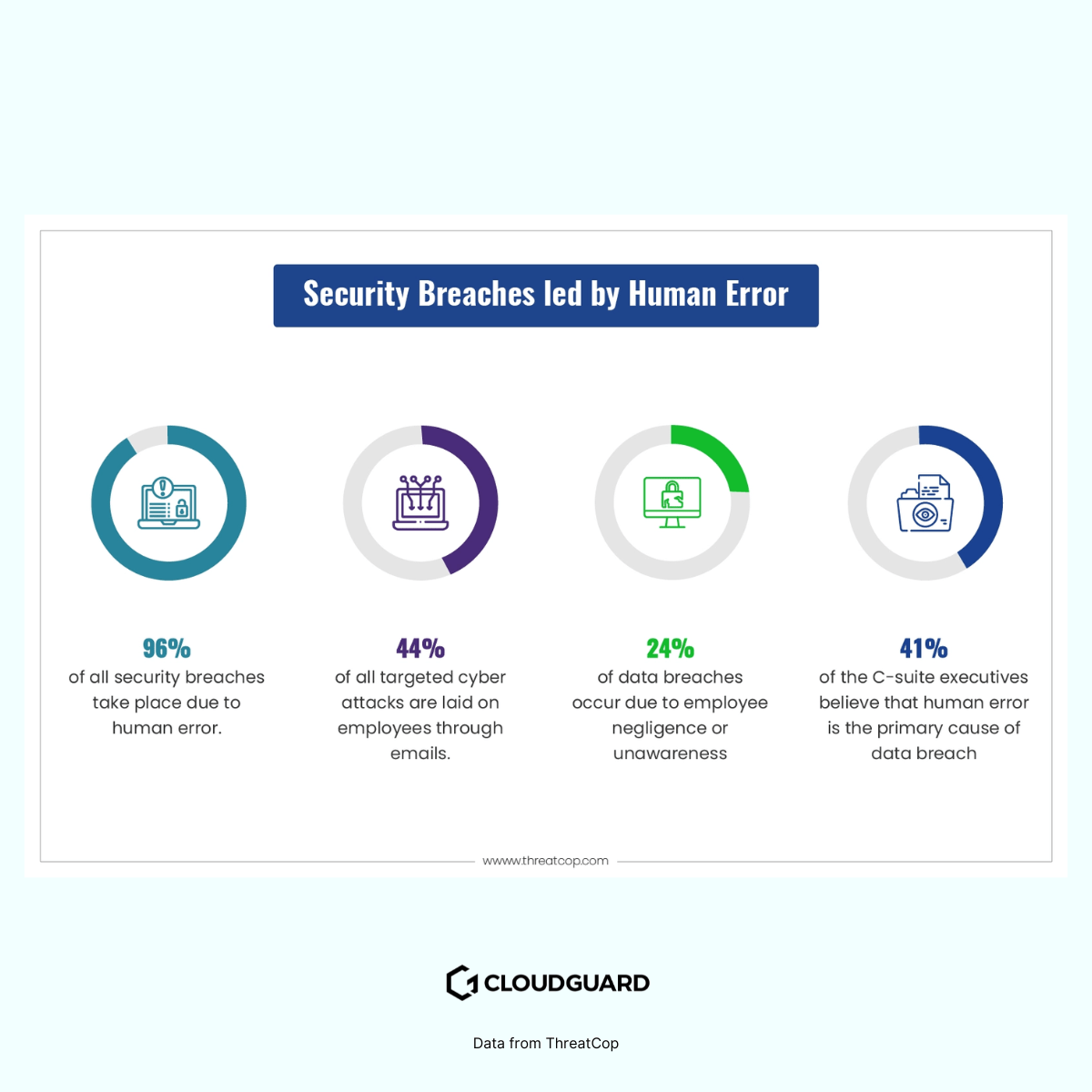
Despite advances in technology, organisations are still vulnerable to data breaches caused by human error and insider threats. Jeff Hancock, Professor at Stanford University, found that 88% of data breaches are due to employee error. According to an IBM Security study, that number is closer to 95%.
Think about the consequences.
Employees can accidentally click on malicious links in phishing emails, misuse sensitive data or unwittingly support social engineering attacks.
The role of human error
Despite solid technical protection measures, human error leads to vulnerabilities that are exploited by attackers. Whether through innocent mistakes or poor judgement, employees can inadvertently compromise the security posture of their organisation.
Threatcop found that 44% of security breaches caused by human error start with email.
Worrying, isn’t it?
Stanford University’s findings highlight the prevalence of human-caused cybersecurity vulnerabilities. These findings highlight the importance of incorporating the human factor into cybersecurity strategies.
What is the solution?
To mitigate this risk, you should offer cybersecurity training to all employees.
Creating a security-concious culture
To effectively address this challenge, it’s important that all employees are trained in cybersecurity.
Take a moment to consider the impact.
Regular training programmes enable employees to recognise and report potential threats, promote a culture of security awareness and empower them to actively participate in maintaining a safe environment.
Implementing strict access controls and monitoring user activity also helps to quickly identify and mitigate insider threats.
By taking full account of the human factor alongside technological protection measures, organisations can strengthen their cyber security against evolving threats.
Isn’t it time to recognise and mitigate the impact of human error in cyber security?
5. Inadequate incident response planning
Incident response is a critical element of cybersecurity, yet many traditional strategies suffer from undefined and untested incident response plans.
But why is it so important?
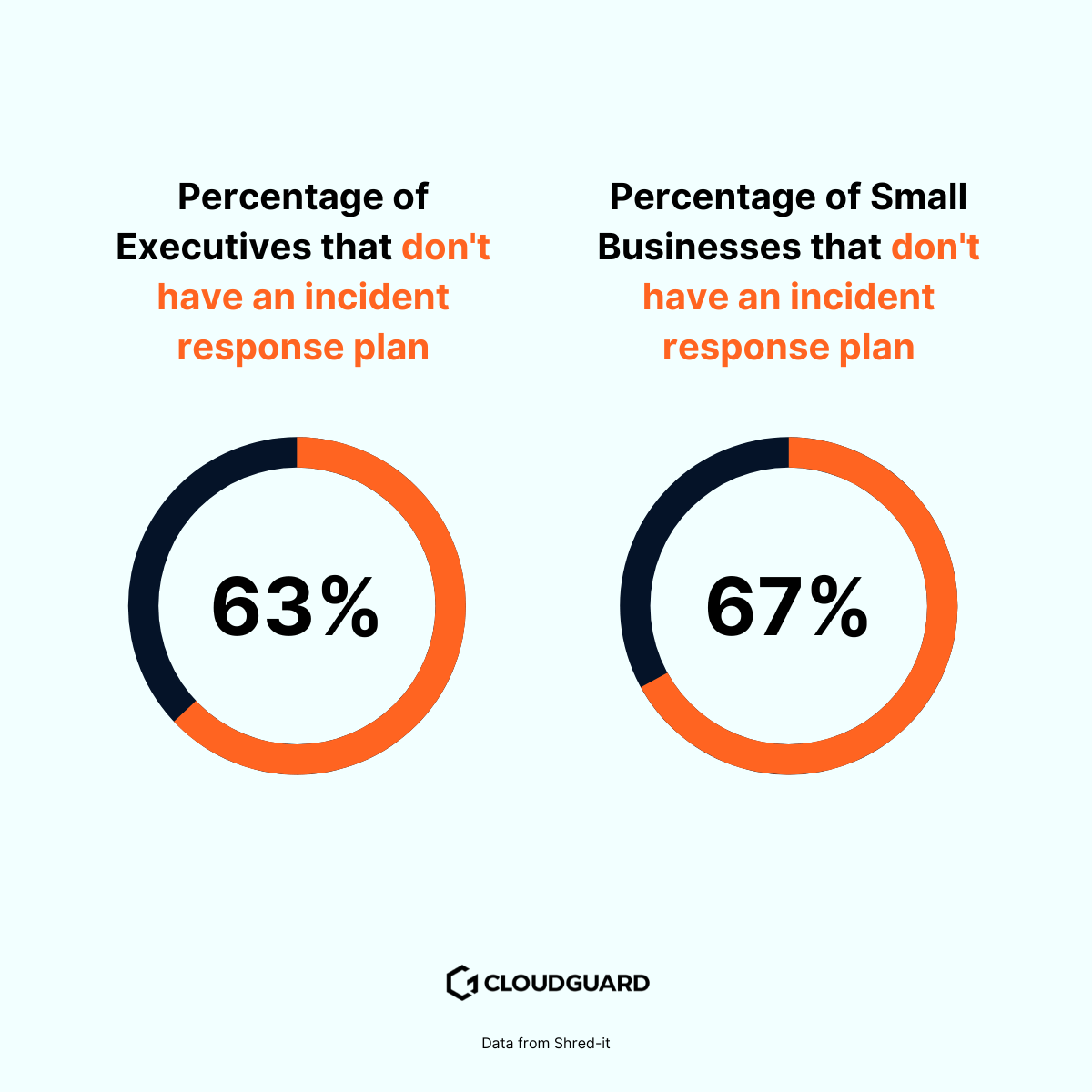
Without a comprehensive plan, it’s difficult for organisations to effectively detect, contain and remediate cyber incidents. Shockingly, a recent report by Shred-it found that 63% of executives and 67% of small businesses in the US don’t have an incident response plan.
That’s a big gap, isn’t it?
Why not having a plan is a big deal
The lack of clearly defined incident response plans leaves organisations vulnerable to extended downtime and greater damage from cyberattacks. Without clear protocols, response actions can be delayed or ineffective, exacerbating the impact of incidents.
Are you worried about the consequences?
The statistics speak for themselves. The report’s findings highlight a widespread problem: the majority of organisations aren’t adequately prepared for cyber incidents. This gap highlights the urgent need to improve incident response capabilities.
What can be done about it?
Modern approaches to incident response
To improve incident response capabilities, it’s important to invest in cybersecurity solutions with automated incident response capabilities.
Automated responses can quickly identify and contain threats, limit their impact and prevent further spread across the network.
Regularly conducting incident response drills and tabletop exercises also ensures that security teams are well prepared to deal with real cyber incidents efficiently.
By practising and refining incident response procedures, organisations can mitigate the impact of cyber-attacks and maintain operational resilience.
Isn’t it time we prioritised comprehensive incident response planning in our cyber security strategies?
6. Failing to prioritise data protection
While protecting external borders is crucial, traditional cybersecurity strategies often overlook the importance of directly protecting the data itself.
Have you ever wondered why this is so important?
Erick Nordman,co-founder and Chief Technology Officer at ZEDEDA, backed this up by saying:
CISOs must approach security at the edge from a broader perspective than they do in the data center or cloud. This means taking into account the business priorities of OT, which may include safety, efficiency, and disconnected operation, and IT, which includes data protection, privacy, and compliance.
Organisations accumulate large amounts of sensitive data, the security of which is crucial to prevent data breaches and regulatory violations.
What neglecting data security can mean
Traditional strategies often focus on protecting the perimeter, leaving the actual data unprotected. This negligence increases the risk of data breaches and non-compliance.
Ben Michael is the VP of Operations at Michael & Associates said:
Businesses often overlook the importance of the simplest, most basic security measure when it comes to cybersecurity…their passwords. They’ll have the same short, easy-to-guess password across all of their accounts.
Are you worried about your data?
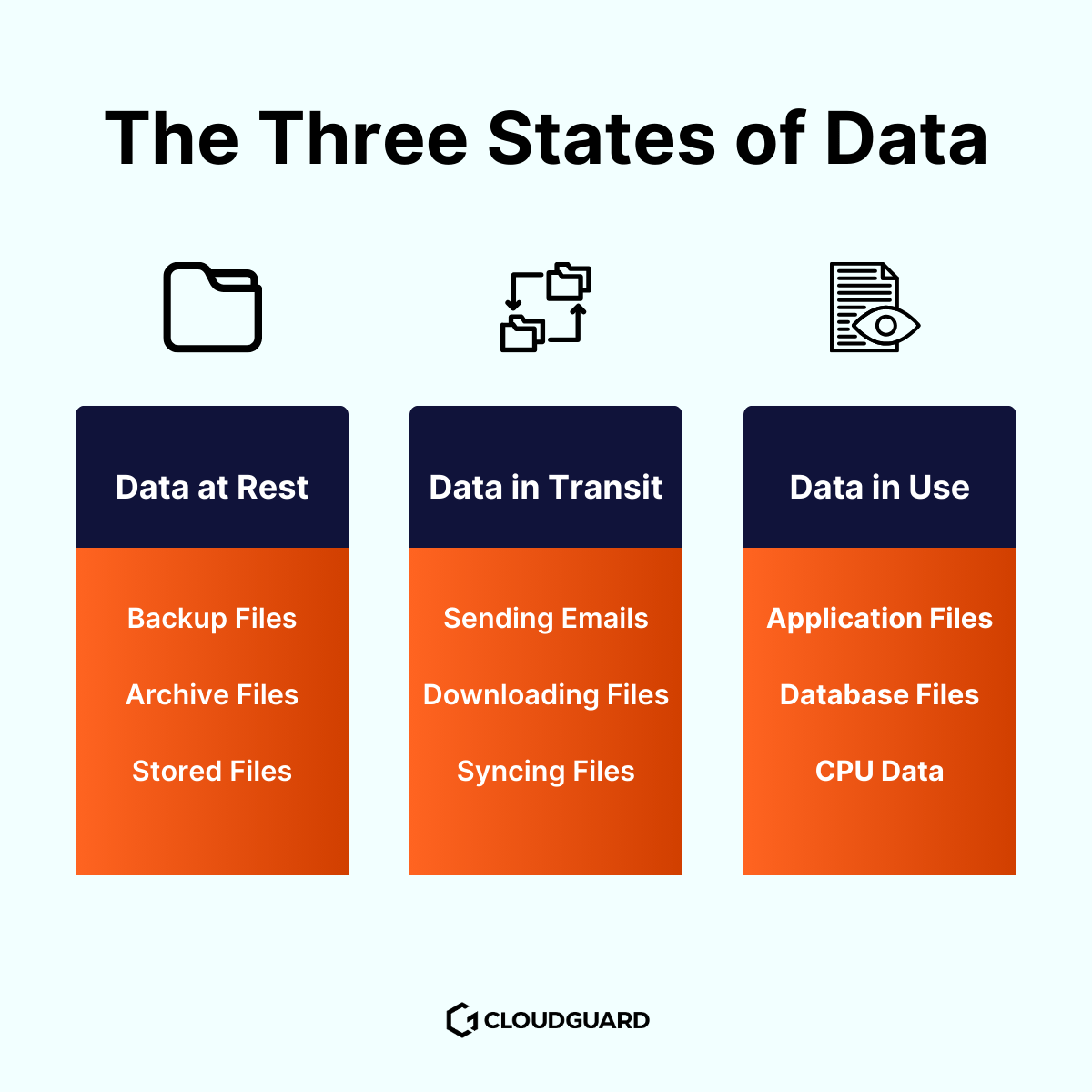
Encrypting data both in transit and at rest is essential. This ensures that data remains unreadable and unusable even if attackers gain unauthorised access and preserves its integrity.
What steps can you take?
How to improve your data security
- Encrypt data in transit using HTTPS and secure protocols like TLS to prevent interception.
- Use full-disk encryption or database encryption to protect data at rest on devices and servers.
- Ensure strong key management practices to safeguard encryption keys. Regularly update and audit encryption methods to maintain security.
In addition, regular monitoring of data usage and user activity helps to detect abnormal access patterns and potential data exfiltration attempts at an early stage.
By prioritising robust data protection strategies, organisations can effectively protect sensitive data against evolving cyber threats and regulatory requirements.
Isn’t it time we focused more on protecting our data directly?
The Rise of Managed XDR – A Game-Changer for the Cybersecurity Revolution
In response to the shortcomings of traditional cybersecurity strategies, a transformative solution has emerged that is revolutionising the way companies like yours protect their digital assets.
Managed Extended Detection and Response (MXDR) is a ground-breaking approach.
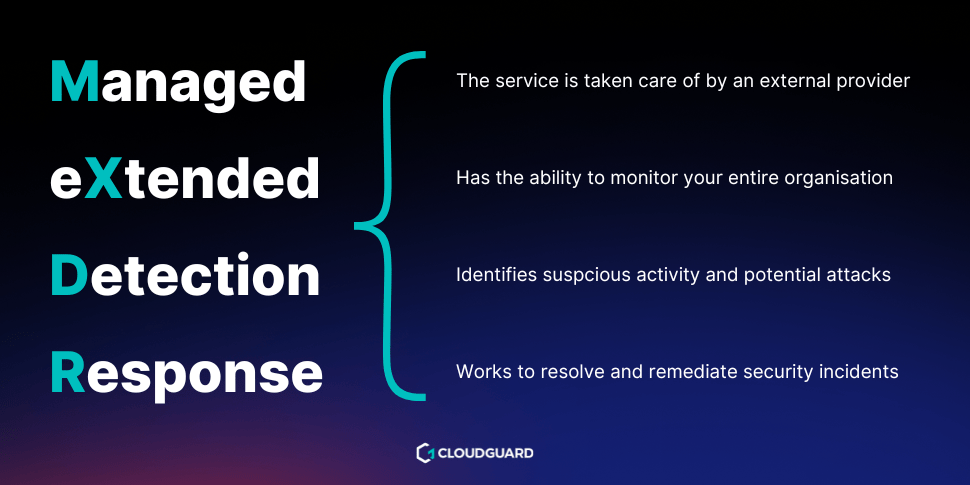
By overcoming the limitations of traditional security measures, MXDR gives you the upper hand in the fight against cyber threats.
This cybersecurity revolution enables organisations to improve their security posture and effectively protect their digital assets against evolving cyberthreats.
Comprehensive threat detection and response
MXDR represents a significant leap forward from traditional security solutions by offering comprehensive threat detection and response capabilities.
Unlike conventional strategies that focus on individual security tools operating in silos, MXDR integrates data from multiple sources, such as endpoints, networks, cloud environments, and applications. This 360 approach provides security teams with a unified view of your business’ security posture.

The end result? They can detect and respond to threats more effectively.
Through continuous monitoring and real-time threat analysis, MXDR leverages advanced analytics, AI, and machine learning to detect suspicious behaviour and potential threats across the entire attack surface.
This proactive defence approach allows you to stay ahead of the rapidly evolving threat landscape and thwart attacks before they cause significant damage.
Automated incident response and demediation
One of the biggest advantages of MXDR is its ability to automate incident response and remediation.
Traditional cybersecurity strategies often rely on manual intervention, causing delays in spotting and stopping threats. MXDR changes this by automating responses based on set policies and playbooks.
When a threat is detected, MXDR can automatically isolate affected devices, block malicious traffic, and apply necessary patches or updates. This quick action reduces the time attackers spend in your network. It minimises damage and data exposure.
Additionally, automating these tasks frees up your security team.
They can focus on strategic decisions and proactive threat hunting instead of repetitive manual work. This shift allows for more effective and efficient cybersecurity management.
Intelligent threat hunting and analysis
MXDR’s advanced analytics capabilities extend beyond automated incident response, enriching security teams with intelligent threat hunting and analysis tools.
These features enable cyber security professionals to proactively seek out potential threats and uncover hidden malicious activities within your network.
By conducting in-depth investigations and correlating data from various sources, MXDR helps identify the root cause of incidents and potential attack patterns. This level of visibility enhances the your overall security posture.
This means you can proactively close security gaps and prevent similar incidents in the future.
Scalability and cost-effectiveness
Conventional cyber security strategies often require significant investment in hardware, software and ongoing maintenance.
MXDR, on the other hand, offers a scalable and cost-effective solution for organisations of all sizes. By utilising a cloud-based infrastructure and managed security services, you can benefit from enterprise-grade security without the need to manage complex systems in-house.
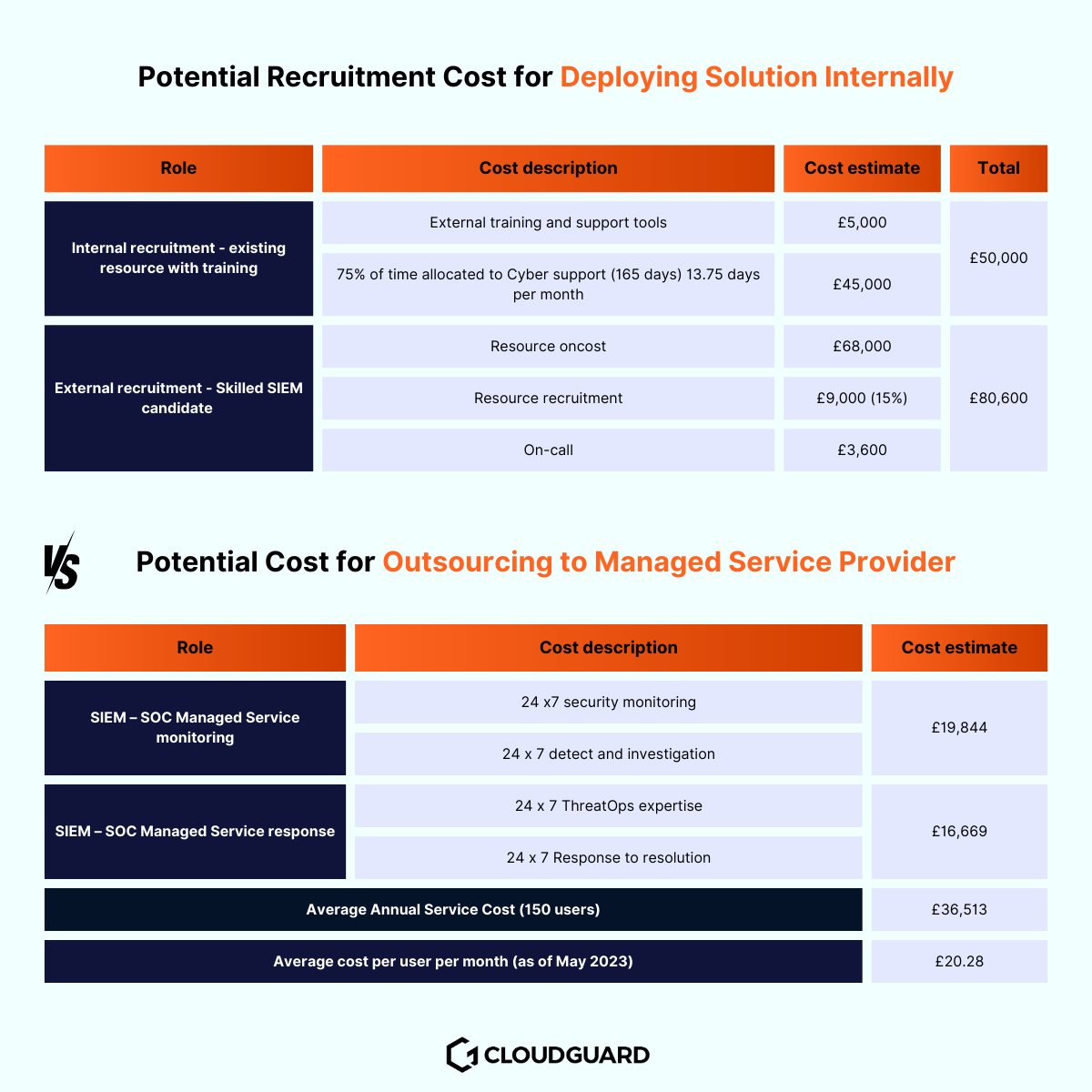
MXDR providers offer round-the-clock monitoring and support. This gives you access to a team of cybersecurity experts without the overheads of an in-house security team.
MXDR’s pay-as-you-go model also ensures that you only pay for the services you need. This makes it an attractive option if your organisation needs robust cybersecurity on a budget.
Final thoughts on the cybersecurity revolution
As the cybersecurity landscape continues to evolve, traditional approaches to protecting digital assets are no longer sufficient.
Conventional strategies don’t have the necessary capabilities to deal with the sophisticated and relentless modern cyber threats. Utilising services such as CloudGuard PROTECT Managed XDR provides you with a transformative solution that overcomes the limitations of traditional cyber security strategies.
MXDR’s comprehensive threat detection and defence capabilities, automated incident response and remediation, intelligent threat hunting and cost-effective scalability make it an ideal choice. Especially if you want to improve your cyber security.
With MXDR, your organisation can stay one step ahead of cybercriminals, protect your sensitive data and ensure the continuity of your operations in the face of ever-evolving cyber threats. Don’t be held back by conventional cybersecurity strategies.
Join the cybersecurity revolution. Invest in MXDR to strengthen your defences and move confidently into the future.